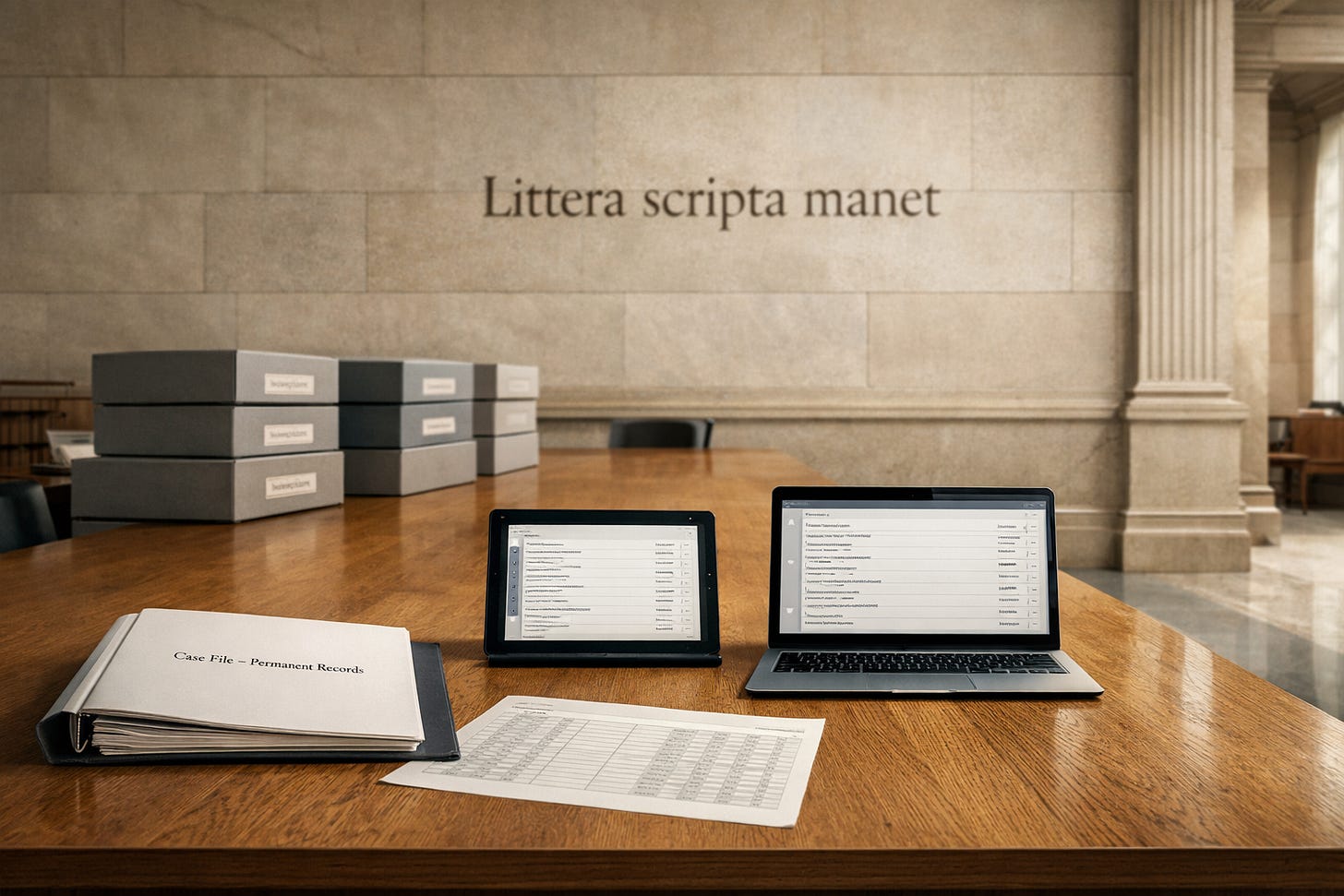
Case Files, Containers, and Control
What NARA’s New Guidance Gets Right—and What It Leaves Unsaid
On September 17, 2025, the National Archives and Records Administration (NARA) issued AC 33.2025, a memorandum to Federal Records Management Contacts announcing an update to Appendix A of NARA Bulletin 2014-04. The update formally added “Case Files” as a media type in NARA’s acceptable format guidance and relocated the existing guidance for PDF Collections under this new category.
On the surface, this looks like a tidy reclassification. In reality, it represents a subtle but important policy shift: aggregation itself is now being governed as a transfer object, not merely tolerated as an implementation detail.
That shift aligns with how federal recordkeeping actually works. It also exposes unresolved tensions between operational guidance and archival theory—particularly when viewed through the lens of international records management standards.
From File Formats to Assemblages
Federal programs rarely produce records as isolated artifacts. Investigations, adjudications, court proceedings, enforcement actions, medical reviews, and benefits determinations all generate multi-format assemblages that accumulate over time. These assemblages—what practitioners routinely call case files—have long existed in practice but only implicitly in policy.
By explicitly defining a case file as:
“a collection of records that relate to a specific matter, individual, event, or administrative action,”
NARA acknowledges that the evidentiary unit is no longer the single file. Context emerges from relationships among records, not from compliance with format alone.
Relocating PDF Collections under the Case Files category reinforces this point. PDF Collections are no longer treated as a neutral format option. They are reframed as mechanisms for packaging aggregated records, with the corresponding risks and controls.
Aggregation as a Risk Vector
The guidance is explicit that case files elevate the risk of inadvertently releasing personally identifiable information (PII), controlled unclassified information (CUI), or national security–related content. This is an important reframing.
Risk is no longer attributed solely to content. It is attributed to assembly and scale.
In response, NARA requires that each embedded file be individually visible, indexed, and labeled for access restrictions. This approach reflects a growing recognition that container-level controls are insufficient when records are distributed as large, heterogeneous sets.
Yet this is where conceptual clarity begins to fray.
Where Is the Record?
The guidance requires that case files “relate to one another as components of a record,” but it never resolves a foundational question:
Is the case file itself the record?
Or are the embedded files the records, with the case file functioning only as a transfer wrapper?
Operationally, NARA treats the embedded files as the primary units of control—mandating per-file checksums, creation and modification dates, and access restriction labels. Conceptually, however, the case file is positioned as the meaningful archival object.
This ambiguity is not trivial. Appraisal, access review, FOIA processing, and long-term preservation strategies all depend on where record identity is understood to reside. The guidance assumes agencies can navigate this duality without an explicit model.
The ISO Perspective: Why “Case File” Is Not Defined
This ambiguity becomes clearer when viewed against ISO records management standards.
There is no explicit ISO definition of “case file.” Core standards such as ISO 15489-1 (Records management — Concepts and principles), ISO 30300 (Management systems for records — Fundamentals and vocabulary), and ISO 16175 (Functional requirements for records systems) deliberately avoid the term.
This is not an oversight. It reflects a design choice.
ISO standards treat case files as instantiations of records aggregation, not as a universal record type. They focus on:
relationships among records,
accumulation over time,
linkage through metadata,
and management of aggregations as outcomes of business activity.
In ISO terms, a case file is best understood as a records aggregation documenting a discrete business activity, governed by context, metadata, and controls—not by its packaging.
ISO 16175 comes closest operationally, requiring records systems to support aggregation, manage relationships, and apply controls at both aggregation and component levels. In practice, many systems implement this as “case file functionality,” even though the standard remains terminology-neutral.
In other words: ISO keeps aggregation conceptually abstract; NARA has made it operationally concrete.
That choice has consequences.
Metadata as Control Infrastructure
The required embedded-file index is more than descriptive metadata. It functions as a compliance infrastructure.
Checksums establish fixity. Dates provide provenance signals. Access restriction labels replace technical controls once passwords and permissions are removed. Trust is asserted through metadata rather than enforcement mechanisms.
This aligns with digital preservation practice and ISO principles around authenticity and integrity. At the same time, it assumes a level of metadata maturity that many federal programs—especially those managing legacy or hybrid case files—do not yet have.
The guidance offers no tiered approach, no allowance for inferred or reconstructed metadata, and no risk-based differentiation. “Mandatory” is absolute, even where reality is not.
PDF Collections: A Constrained Endorsement
NARA continues to accept PDF/A-3 and PDF/A-4f for case files, but under strict conditions: no folders, no nested embedded files, no hidden content, no active security, full font embedding throughout.
These constraints are understandable from an ingest and transparency perspective. They also raise a legitimate question: if PDF Collections must be stripped of most container-like behavior, are they the right abstraction for case files at all?
What remains is effectively a flat package with a viewer—less a file system, more a manifest. Alternative aggregation models familiar to digital preservation practitioners remain outside the preferred framework, reinforcing a lingering reliance on PDF as a comfort zone even when it functions primarily as a wrapper.
Security by Declaration
Agencies are required to deactivate all security controls before transfer and rely entirely on metadata labels to signal sensitivity. From NARA’s perspective, this is necessary for access and preservation. From an agency perspective, particularly for law enforcement, health, or benefits programs, it introduces unease.
The guidance does not meaningfully address chain-of-custody risk, interim exposure, or threat modeling during transfer. Security is displaced from enforcement to declaration, without a fully articulated trust model.
Governing the Handoff, Not the Horizon
Like much of NARA’s format guidance, AC 33.2025 governs ingest, not long-term evolution. It says little about how case files might be restructured, migrated, or re-expressed as formats age and access expectations change.
ISO standards are explicit that preservation is a lifecycle concern. NARA’s guidance remains focused on the moment of transfer.
Why This Matters
By issuing AC 33.2025, NARA has done something important: it has acknowledged that case files are now a primary unit of federal digital recordkeeping. Aggregation is no longer incidental. It is governed.
At the same time, by defining what ISO intentionally leaves abstract, NARA has hardened a flexible concept into a specific transfer object. That brings clarity—but also constraint.
Case files have finally been named. The harder work—articulating a coherent archival theory of digital aggregation that spans systems, transfer, and long-term preservation—still lies ahead.
This guidance is worth reading closely, not just for what it prescribes, but for what it reveals about where federal records governance is headed—and where it is still catching up.


Brilliant breakdown of NARA's shift here. The ambguity around whether the case file or its embedded components constitute the 'real' record is something I ran into when workingwith legacy litigation files, it made appraisal borderline impossible. Treating aggregation as a governed transfer object feels overdue but the lack of tiered metadata requirements seems risky.